The Waste of Mistrust
Who can you trust? That is a question that individuals and organisation’s spend a lot of time considering in today’s society.
Increasingly it seems that the assumption built in to most of our lives is that we can trust pretty much no-one. Almost every transaction we do is wrapped in passwords and privacy checks on the assumption that we are all potential hackers and identity thieves.
In Lean Thinking, we typically define waste as an activity that does not add value to the customer. Mistrust is a great source of non-value added waste. There are lots of examples of the waste of mistrust, but the ones I have identified are:
1) Overly Restrictive Account Access. Have you tried to call your bank or telecommunications company lately? After you go through the labyrinthine range of call options (another form of waste – have you thought how much time gets wasted redirecting people who end up with the wrong operator) and and get to the person you want, you are usually faced with a battery of “privacy” questions before you can access your own or you company account. I recently was locked out of my phone account, calling on my own phone, with all my account details, including the “password”, because the (correct) date of birth I provided for myself did not match the incorrect one they had on their records.
2) Excessive secrecy and Data segregation: How much effort does your organization put in to keeping information from people? Do people spend their days trying to get access to information or gain approvals in order to do their jobs? Some business systems excel in segregation of responsibilities. Great accounting theory, but how much time is spent waiting for transactions to be authorized and how thorough is the check applied when they are.
3) One sided contracts: Large companies, especially in construction often apply onerous contracts on their suppliers including large liquidated damages clauses. These clauses are based on the assumption that suppliers can not be trusted to deliver on time. They are applied universally, even when a supplier may have a long history of on-time completion or delivery. The damages clauses then tend to be passed on to upstream suppliers and drive highly risk-averse behavior that ultimately drives up costs.
4) Interpersonal and interdepartmental mistrust: In many organisations the level of trust between teams is poor. For example, sales may not trust production to deliver, so will falsely inflate forecasts leading to over-production. Production in turn may not trust purchasing or suppliers leading to excessive inventory and hoarding of inventory. As for finance, they probably see it as their job not to trust anyone, so will check and recheck everything!
When you think about your life and your organisation, I am sure you will see that mistrust is an enormous source of waste. So how can we reduce the waste of mistrust?
I think at the core of the waste of mistrust is a current misunderstanding of the management of risk. When we identify a risk, we should assess that risk before we try to mitigate it. That means we need to assess the likelihood or frequency of occurrence and the severity when the problem does occur. Often there are other checks in place to mitigate the risk. For example, in the case of my phone, I could have been someone trying to defraud my account, which is the reason for the “privacy” protection. However, the likelihood of this was very low given that I was calling on my own phone (which they could see), was purchasing a service that could only be used for my own phone and I could provide a range of other details about our account that someone who had stolen my phone would be unlikely to access. In terms of severity, the service (international data) that I was purchasing was capped and only worth $150, so the amount I could spend was relatively small. In this case the likelihood of fraud was very low, the consequence of such a fraud was relatively small and so the cost and inconvenience caused by the “privacy” checks were clearly unjustified. A similar test could be applied to each of the examples above. Instead there is a tendency to believe every risk should be mitigated, no matter how likely or severe.
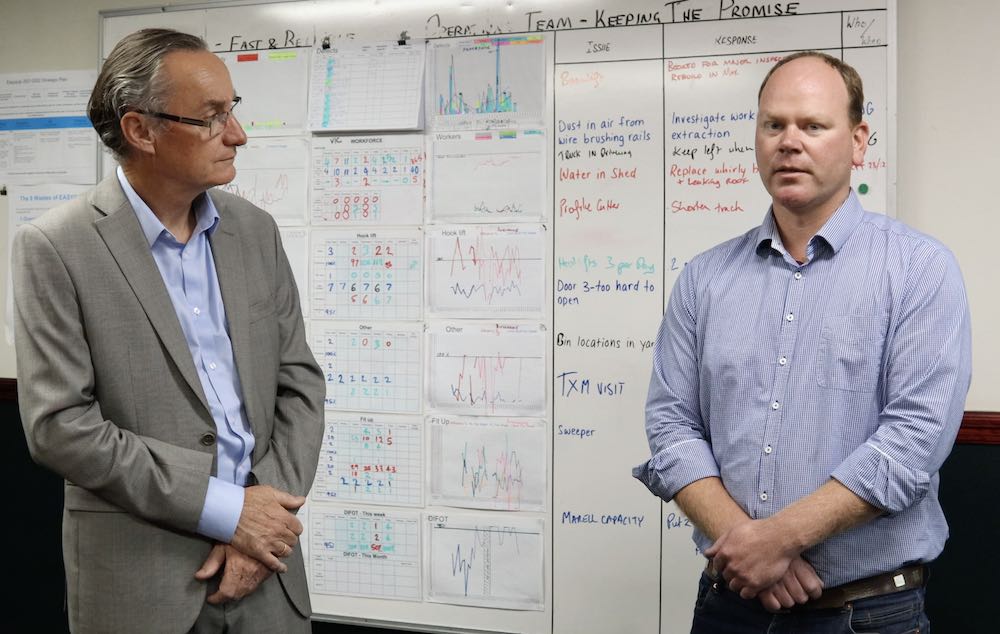
Another way to reduce mistrust is through data and credible metrics. If production can demonstrate that they deliver on time and in full. Then sales may be less likely to over-forecast – particularly when it is shown that over-forecasting typically makes on-time delivery worse rather than better. Likewise, a construction supplier with a history of good planning and on time completion, should be rewarded with exemption from liquidated damages clauses. This will lead to lower project costs, better and more open relations and potentially earlier completion as “padding” in the schedule is removed.
Recognize that not everyone is a crook and that crooks are very good at getting around bureaucratic checks and approvals. In my 30 year career working with thousands of people, I have encountered one case of fraud and am yet to come across a proven case of employee sabotage. These things are very rare. In a developed society most people try to do the right thing. Therefore the overwhelming majority of errors and variances are not deliberate. They are caused by people and process issues. In Lean we talk about quality at the source where each person is responsible for the quality of their output and leaders support people to over come problems. When we have a variance or a quality problem, before we apply extra checks and authorization levels, we need to apply our problem solving skills to find and address the root cause and prevent the problem re-occurring. We might need some extra checks or audits in the short term, but these should only continue if we continue to find problems.
I am not naive enough to believe that the world does not have its share of people who should not be trusted. The constant stream of internet scams that arrive via email is evidence of that. However, mistrust is becoming increasingly institutionalized. Perhaps we should stop and think about the cost before we add another layer of passwords, privacy checks and authorizations to our lives and our businesses.
Learn More about Other Office Wastes
Learn About How to Sustain Lean in the Office